How to Add Proftpd in CentOS 7 for ftp access.
Step 1: Add the EPEL Repository
ProFTPD is part of Extra Packages for Enterprise Linux (EPEL), which is a community repository of non-standard packages for the RHEL distribution. First, we’ll install the EPEL repository:
# rpm -iUvh http://dl.fedoraproject.org/pub/epel/7/x86_64/e/epel-release-7-5.noarch.rpm
Step 2: Install ProFTPD
Let’s update first:
# yum -y update
Then let’s install ProFTPD and any required packages:
# yum -y install proftpd
Step 3: Configure ProFTPD
For a refresher on editing files with vim see: New User Tutorial: Overview of the Vim Text Editor
Let’s edit the configuration file for ProFTPD:
# nano /etc/proftpd.conf
Change the ServerName to the hostname of your server. In the case below, ftp.domainname.com is an example:
ServerName “ftp.domainname.com”
Enabling TLS In ProFTPD
Add and modify the lines as below.
# nano /etc/proftpd.conf [...] DefaultRoot ~ !adm PassivePorts 60000 65535 [...] # TLSEngine on TLSRequired on TLSRSACertificateFile /etc/pki/tls/certs/proftpd.pem TLSRSACertificateKeyFile /etc/pki/tls/certs/proftpd.pem TLSCipherSuite ALL:!ADH:!DES TLSOptions NoCertRequest TLSVerifyClient off TLSRenegotiate ctrl 3600 data 512000 required off timeout 300 TLSLog /var/log/proftpd/tls.log # # TLSSessionCache shm:/file=/var/run/proftpd/sesscache # # [...]
Exit and save the file with the command :wq .
Restart the ProFTPD service:
# systemctl restart proftpd
Then set the ProFTPD service to start at boot:
# systemctl enable proftpd
And verify your work by checking the status of ProFTPD:
# systemctl status proftpd
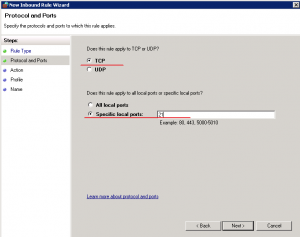
Step 4: Allow ProFTPD Through the Firewall
Allow the default FTP port, port 21, through firewalld:
# firewall-cmd --permanent --add-port=21/tcp # firewall-cmd --add-port=60000-65535/tcp --permanent
And reload the firewall:
firewall-cmd --reload
In order to use TLS, we must create an SSL certificate. Create it in /etc/pki/tls/certs, we can generate the SSL certificate as follows:
# openssl req -x509 -nodes -newkey rsa:1024 -keyout /etc/pki/tls/certs/proftpd.pem -out /etc/pki/tls/certs/proftpd.pem
[root@webhost certs]# openssl req -x509 -nodes -newkey rsa:1024 -keyout /etc/pki/tls/certs/proftpd.pem -out /etc/pki/tls/certs/proftpd.pem -nodes -days 365 Generating a 1024 bit RSA private key .++++++ ...........................................................++++++ writing new private key to '/etc/pki/tls/certs/proftpd.pem' ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:US State or Province Name (full name) []:Texas Locality Name (eg, city) [Default City]:Austin Organization Name (eg, company) [Default Company Ltd]:TestCo Organizational Unit Name (eg, section) []:IT Common Name (eg, your name or your server's hostname) []:webhost.domainname.com Email Address []:test@gmail.com
# chmod 0440 /etc/pki/tls/certs/proftpd.pem
Restart:
# systemctl restart proftpd.service